The ability to remotely access a computer on a home network while away from home can often prove very useful.
Employing a technique known as SSH (Secure Shell) tunnelling this article describes how to securely access files on a remote computer using AFP (Apple Filing Protocol) and share that computer’s screen using VNC (Virtual Network Computing).
Table of Contents
- 1. Overview
- 2. Configuring the Router for Port Forwarding
- 3. Enabling Screen Sharing, File Sharing and Remote Login on the Remote Computer
- 4. Establishing an SSH Tunnel
- 5. Using Mac OS X Terminal to Establish the SSH Tunnel
- 6. Using SSH Tunnel Manager to Establish the SSH Tunnel
- 7. Connecting to the Remote Computer
- 8. Sharing the Remote Computer’s Screen
1. Overview
The example described throughout uses Apple hardware: a MacBook, an iMac, an AirPort Extreme and Apple software: Mac OS X Lion 10.7.5, AirPort Utility (see note below). However, it can be adapted for other hardware and software configurations.
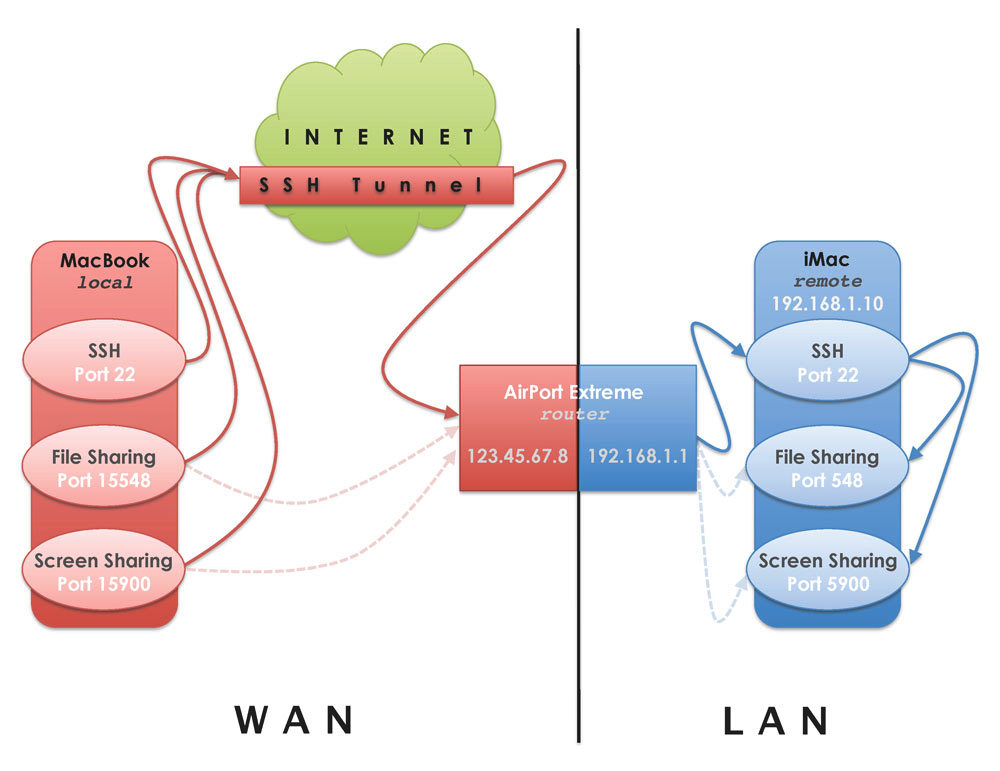
The diagram above depicts a MacBook (local computer) using SSH to connect remotely to an iMac (remote computer) on a home network.
Instead of connecting directly to ports 548 (file sharing) and 5900 (screen sharing) on the iMac, the MacBook tunnels these connections through the SSH connection. This method is useful when circumventing firewalls that can often block ports 548 and 5900. In addition, tunnelling these connections through SSH renders them more secure than they would otherwise be.
Before continuing I recommend two things: assigning the home computer you’ll access remotely a static private IP address and providing a static hostname for the Airport Extreme’s dynamic public IP address.
The AirPort Utility screenshots are from version 5.6.x. As of November 2014 the current version of AirPort Utility is 6.3.1. Unfortunately, some functionality available in v5.6.x has been removed from v6.
For Mac OS X Leopard, Snow Leopard and Lion, v5.6.x can be downloaded from Apple. However, on later versions of Mac OS X the AirPort Utility v5.6.x installer may fail.
The AirPort Utility v5.6.1 application without the installer is available here on Corey J Mahler’s site.
2. Configuring the Router for Port Forwarding
The computer I’ll be connecting to remotely is an iMac, which I’ll call the remote computer, on my home network. This remote computer is connected to an AirPort Extreme, which I’ll refer to as the router, and has a static internal IP address of 192.168.1.10. The local computer I’ll be using to connect to the remote computer is a MacBook.
The first task is to configure the router to handle remote connection requests on port 22 from the local computer and send or forward them to port 22 on the remote computer. This is a process known as port forwarding or port mapping. I use AirPort Utility to configure the AirPort Extreme.
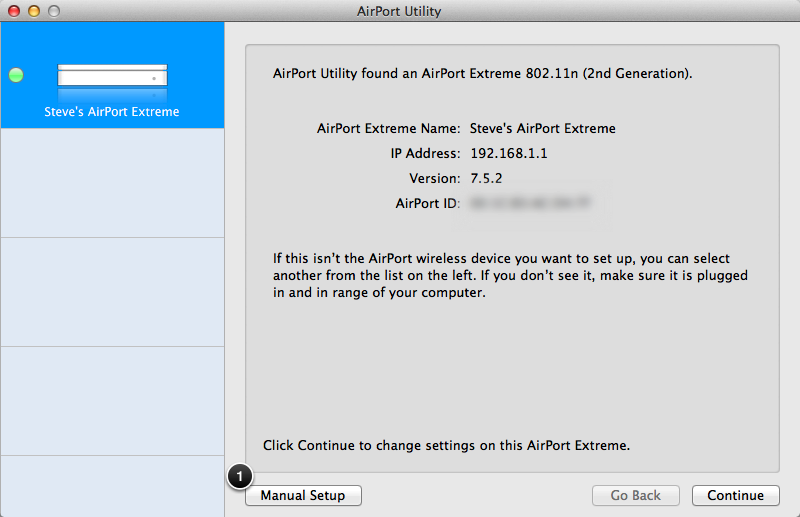
Open AirPort Utility located in the /Applications/Utilities folder.
1. Click on Manual Setup to continue.
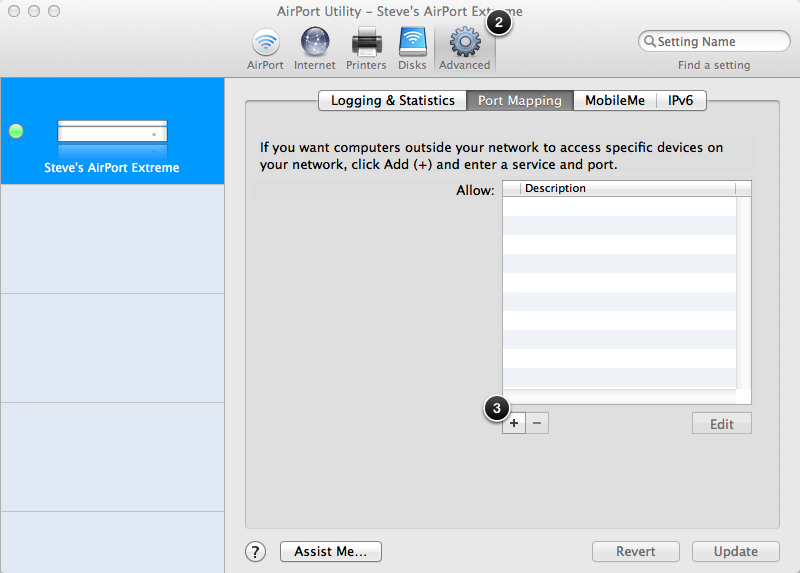
2. Click the Advanced icon.
3. On the Port Mapping tab click + to configure a service and port to forward to.
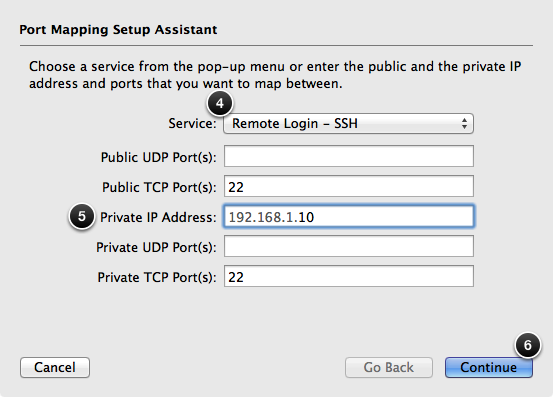
4. Select Remote Login – SSH from the Service drop-down menu. The Public TCP Port(s) and Private TCP Port(s) fields are automatically populated with 22: the default SSH port.
5. Enter the Private IP Address of the computer on the home network you want to access remotely. This ensures that when the router receives an external remote connection request on port 22 it will forward it to port 22 of the computer on the local network with the IP address of 192.168.1.10.
6. Click Continue to go to the next screen of the Port Mapping Setup Assistant.
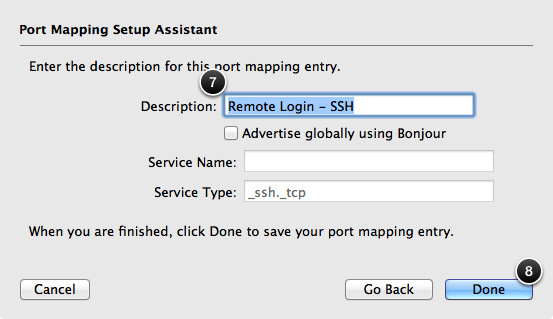
7. The Description is automatically populated with the service name: Remote Login – SSH.
8. Click Done to return to the Port Mapping tab.
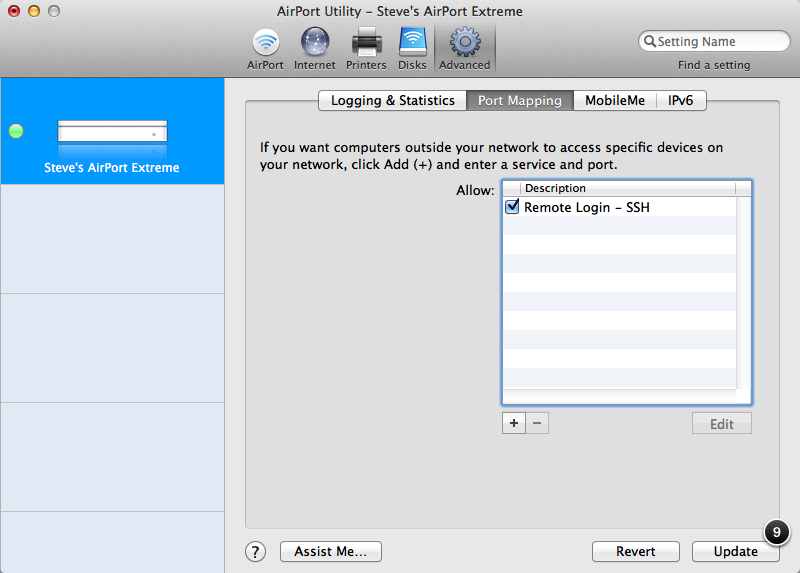
9. Click Update to apply the changes.
3. Enabling Screen Sharing, File Sharing and Remote Login on the Remote Computer
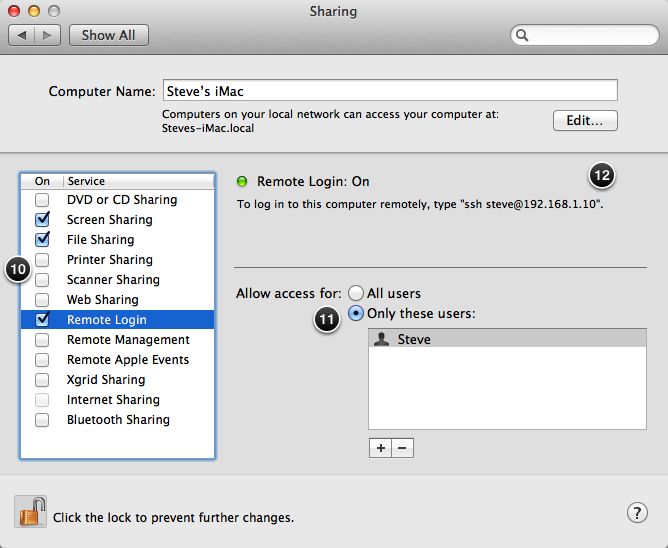
Next, Screen Sharing, File Sharing and Remote Login need to be enabled on the remote computer.
On this computer open System Preferences and click Sharing.
10. Click the Screen Sharing, File Sharing and Remote Login options.
11. For Remote Login I prefer to limit the users who have access.
12. The message To log in to this computer remotely, type “ssh steve@192.168.1.10” is a little misleading. The IP address 192.168.1.10 is only applicable when logging in from another computer on the same local network. Logging in from a computer outside of the local network requires the external public IP address of, in this case, the AirPort Extreme or a hostname that resolves to that IP address. More on that shortly.
4. Establishing an SSH Tunnel
Having configured the router and remote computer we can establish the SSH tunnel from the local computer to the remote computer using either the ssh command in the Mac OS X Terminal application or a GUI front-end to the ssh command such as SSH Tunnel Manager.
5. Using Mac OS X Terminal to Establish the SSH Tunnel
To create the SSH tunnel using the Mac OS X Terminal application open Terminal in the /Applications/Utilities/ folder on the local computer. In the Terminal window type:
ssh -f user@hostname -L 15548:127.0.0.1:548 -L 15900:127.0.0.1:5900 sleep 60
Where;
user is the login name on the remote computer.
hostname is the remote computer’s IP address or name. For information on assigning a static hostname to a dynamic IP address see Resolving a Static Hostname to a Dynamic IP Address Using DynDNS Free.
15548:127.0.0.1:548 is the port:host:hostport parameter where port is the port on the local computer to be forwarded to the given port on the remote computer, host is the localhost on the remote computer and hostport is the port on the remote computer. Using a privileged port, 1024 or below, on the local computer requires the use of sudo.
My example uses two port:host:hostport parameters each proceeded by the -L option. The first: -L 15548:127.0.0.1:548 is for AFP, the second: -L 15900:127.0.0.1:5900 is for VNC.
sleep 60 will terminate the tunnel after the allotted time, in this case 60 seconds, but only if there’s no active connection. The sleep option will not work when the -N option is included in the ssh command as this option disables remote commands.
The first time the SSH tunnel is established you’ll be prompted with:
The authenticity of host 'hostname (12.345.67.890)' can't be established. RSA key fingerprint is xx:xx:xx:xx:xx:xx:xx:xx:xx:xx:xx:xx:xx:xx:xx:xx. Are you sure you want to continue connecting (yes/no)?
Type yes and press enter.
You’ll be prompted with the warning:
Warning: Permanently added 'hostname,12.345.67.890' (RSA) to the list of known hosts. Password:
Enter the password for the user on the remote computer you’re logging in as and press enter.
Now that the SSH tunnel is established and having specified a sleep parameter of 60 we have only 60 seconds to make a connection to the remote computer before the tunnel disappears. The presence of the tunnel can be confirmed by typing:
ps -ax | grep ssh
If the tunnel is present the results will include a line of text similar to the highlighted line:
2234 ?? 0:00.05 /usr/bin/ssh-agent -l 6455 ?? 0:00.00 ssh -f user@hostname -L 15548:127.0.0.1:548 -L 15900:127.0.0.1:5900 sleep 60 6469 ttys000 0:00.00 grep ssh
At this point the SSH tunnel could be manually closed by terminating the process. While there seems little point in establishing the tunnel only to manually close it shortly after, it’s useful to know that it can be done and how to do it. To manually close the SSH tunnel type:
kill 6455
Where 6455 is the process number of the SSH tunnel.
On a side note, the list of known hosts is stored in the file known_hosts in the hidden folder ssh in your user directory. To see the contents of known_hosts type:
cat ~/.ssh/known_hosts
Although not necessary in this situation a specific entry for a known host e.g. 12.345.67.890 can be removed by typing:
ssh-keygen -R 12.345.67.890
The next time you establish a tunnel to this host you’ll be prompted to authenticate again.
6. Using SSH Tunnel Manager to Establish the SSH Tunnel
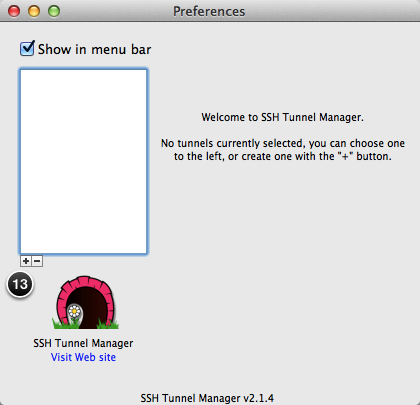
An alternative to using Terminal to establish the SSH tunnel is SSH Tunnel Manager.
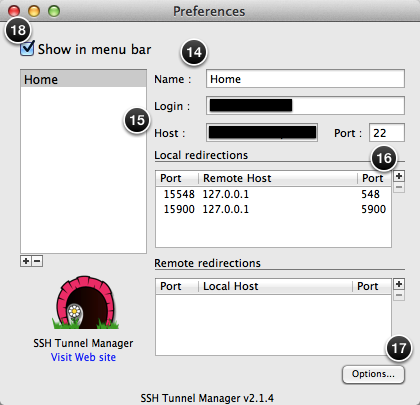
Having opened SSH Tunnel Manager, press ⌘, to open the Preferences window.
13. Click + to create a new SSH tunnel configuration.
14. Enter a Name for the SSH tunnel configuration.
15. Enter the Login and Host details. These correspond to user and hostname in our Terminal command. Set the Port to 22 the default SSH port.
16. Click + to create a new Local Redirection and enter the Port, Remote Host and Port details. These correspond to the port:host:hostport combination in our Terminal command.
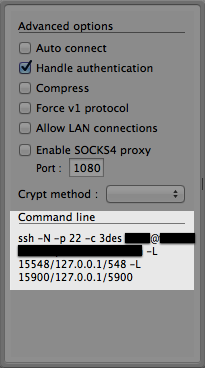
17. Before closing the Preferences window click Options to see the command line equivalent of the SSH tunnel configuration. This is similar to our Terminal command.
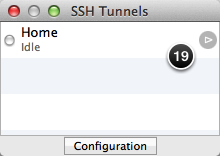
18. Close the Preferences window by clicking at the top-left corner. To establish the tunnel in SSH Tunnel Manager press ⌘T to display the list of tunnel configurations.
19. Click the grey circle to establish the SSH tunnel. You’ll be prompted for the password associated with the Login and Host details on the remote computer.
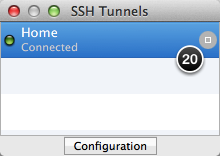
20. To close the active SSH tunnel click the grey circle.
7. Connecting to the Remote Computer
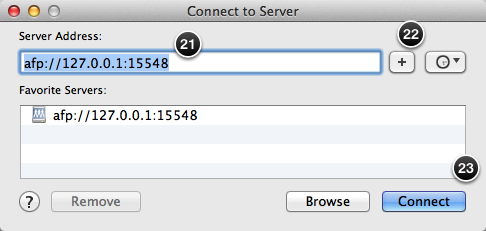
Having established an active SSH tunnel we can now connect to the remote computer. In the Mac OS X Finder press ⌘K for the Connect to Server panel.
21. As we’re connecting to the remote computer using AFP we enter afp://127.0.0.1:15548 for the Server Address where 127.0.0.1 is the IP address of the remote computer and 15548 is the port on the local computer to be forwarded to port 548, the default AFP port, on the remote computer.
22. Click + to add this server address to the list of favourites, if desired.
23. Click Connect to establish the connection to the remote computer. You’ll be prompted to enter a login name and password that exists on the remote computer.
An alternative to using the Connect to Server panel is to enter the following command in Terminal:
open afp://127.0.0.1:15548
24. Select Connect as Registered User.
25. Enter your Name and Password on the remote computer.
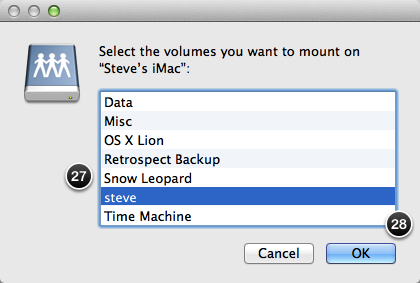
26. Click Connect and you’ll be asked to select a volume on the remote computer to mount on the local computer.
27. Select a volume on the remote computer to mount.
28. Click Connect and the selected remote volume will be displayed in the Finder of the local computer.
8. Sharing the Remote Computer’s Screen
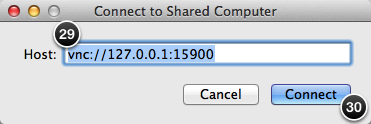
To share the remote computer’s screen we can use the Screen Sharing application located in /System/Library/CoreServices/.
29. As we’re connecting to the remote computer using VNC we enter vnc://127.0.0.1:15900 for the Host: where 127.0.0.1 is the IP address of the remote computer and 15900 is the port on the local computer to be forwarded to port 5900, the default VNC port, on the remote computer.
30. Click Connect to share the remote computer’s screen. You’ll be prompted to enter a login name and password that exists on the remote computer.
An alternative to using the Screen Sharing application is to enter the following command in Terminal:
open vnc://127.0.0.1:15900
31. Select Connect as Registered User.
32. Enter your Name and Password on the remote computer.
33. Click Connect and you’ll be asked to select a volume on the remote computer to mount on the local computer.


I have been trying endlessly to Mount our office network Mac volumes using afp over the Internet on Catalina. I wants got it to bring up the username and password box. That’s only once and it never connected when I put in the correct username and password. I suspected that my ISP was blocking those ports.
However, due to Covid I have plenty of time on my hands. I pulled out an old blueish gray G4 that has OS X server version five on it set up for exactly this task. When I plugged it in and fired it up, I was able to connect to it over afp over the Internet. I had port 548 forwarded to that G4. At Mouned the volume on my desktop, normally, just as it did years ago. Yes, The iOS 10 servers volume showed up on my home iMac just like I was in my office. It gave me transfer rate of about 20 MB per second.
To connect from the remote computer I would type into the connect to server box fP://url.tld
Why can’t Catalne do this?
Wow
Thank you so much for this! This is the best tutorial I’ve found about remote desktop over a SSH tunnel.
Some notes. Step 29, could be confusing for some. There the remote host is actually “calling home”. 127.0.0.1 is yourself = localhost. But the specified port on that host (“the machine you are using”) is bound to another host through the SSH tunnel. This is the whole idea.
Step 33, does not exist in real life. It looks like it is copied from the text about AFP.
To make this tutorial even more complete. You could make a post about setting up ddclient with Homebrew. Since many free dns hosts doesn’t offer clients (especially not for OS X).
Some other future post could be:
* Reverse SSH to bypass routers with a NAT that you can’t set up.
* Creating non standard SSH ports.
* autossh
And the OS X “Screen Sharing.app” is found in:
/System/Library/CoreServices
I have mine in the Dock 😉
Hey Steve! My Airport Utility doesn’t look like that…I have the latest generation Airport Extreme (the tall rectangular one). In Airport Utility I can’t find an option for Manual Setup, and went through all the other dialog boxes and tabs of my router looking for SSH. Is it still possible? Thanks!
@Esther,
This is a possible explanation. And here’s a link to Apple’s AirPort Utility download page.
Regards, Steve.
Awesome tutorial! Works perfectly. Many thanks!
David
@David,
Glad you found it useful.
Regards, Steve.
Excellent help!
I have a doubt:
We have a TimeCapsule connected to a router provided by our ISP via Ethernet. Is it correct to forward ports only in the ISP router instead of TM, or better forward in both devices?
Thank you for your kind time spent in writing these gems.
@Mauricio,
Forwarding the ports for the Time Capsule should suffice.
Regards, Steve.